The digital transformation brings innovations – sometimes that more and more applications are operated in the cloud. Of course, this has advantages: the maintenance effort, for example, is significantly reduced, which means that costs can also be reduced. But it is also essential to deal with IT security – and we will do that for you in this article. Now that we’ve clarified what serverless applications and cloud computing are, let’s also discuss the pros and cons of serverless security. After tracking down common mistakes, we pass on concrete recommendations and best practice approaches to you.
Table of Contents
Serverless Security: What Does It Mean?
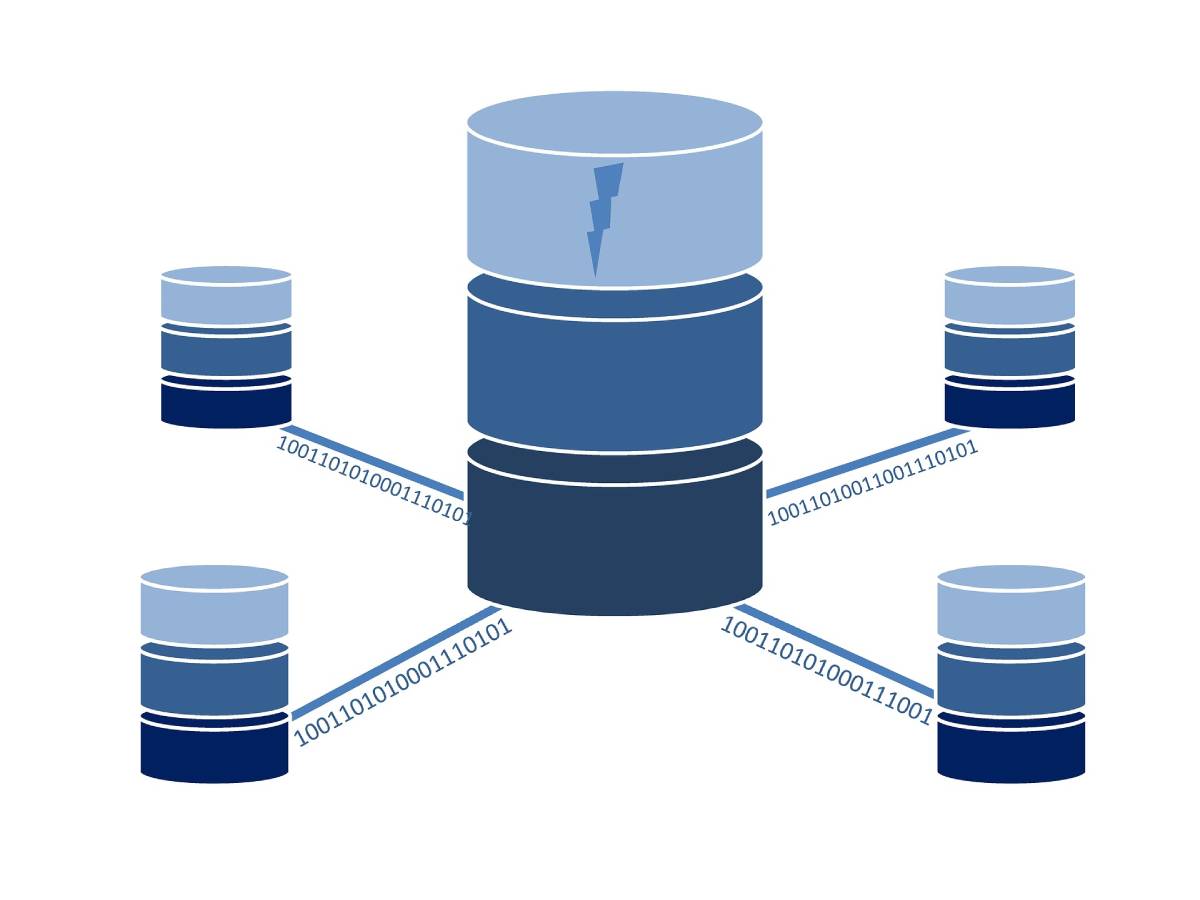
Serverless functions are code snippets executed in an event-based manner in fully managed infrastructures. With serverless architectures, it is possible to set up complex application systems without worrying about managing the infrastructure: cloud providers take on aspects such as scaling, availability, or provisioning. Many new processes, strategic considerations, and tools are required to secure serverless applications. If users continue to build on well-known processes or procedures, security can no longer be guaranteed in the long term.
In the serverless world, an application usually consists of hundreds of functions. Each of them is relatively simple, but when used together, the application results in an overall system that is mainly more complex. As you can already see in this introduction to serverless security, this principle results in many advantages and disadvantages in terms of IT security.
Serverless Security: The Benefits
Let’s first come to the plus points of serverless security: Since cloud providers take care of the security of the cloud server, the operating system, the runtime, and patching, users have significantly more resources at their disposal – this is probably the most visible advantage. Another is the possible exemplary configuration: Serverless architectures significantly increase the number of possible functions. As a result, identity and Access Management (IAM) can also define several roles. This may not seem particularly advantageous to many organizations at first. However, by choosing the right tools and processes, it is possible to build so-called “shrink-wrapped permissions” around each function. This results in further development of the Zero Trust approach: Each part can only access those resources or services that it is permitted to access. This “least privilege principle” prevents numerous cyberattacks on applications when properly configured.
In practice, the large number of rights can confuse and is often circumvented with an allow policy. However, overarching law is not the point because this would open the door to attacks. It is better to find suitable – namely minimal – permissions; the effort is worth it! If the logic of functions changes in time, the rights can be adjusted at any time. This Least Privilege Principle should also be used for access to third-party systems from the cloud: roles with minimal permissions are created and assigned to the appropriately accessing serverless functions.
Existing concepts are often characterized by large containers stuffed with powers and access rights. With the serverless architecture, a rethink helps: a large number of functions ensure that the effect of each one is quite limited – each position is only allowed a small action. Thus, the small parts exist very briefly before they are subsequently reloaded. This has the advantage that attacking functions can only be abused for a short time before they disappear again. Therefore, it is essential to configure the lifespan of positions as straightforwardly as possible so that many attacks are made almost impossible.
The downside of this coin is that attackers also learn that cybercriminals keep attacking again and again if the duration is short. This is known as Groundhog Day Attack or Groundhog Day Attack. Attacks of this type are very noticeable, so detecting them and stopping them is relatively easy.
The logs of the individual microservices increase transparency. Furthermore, control programs have significantly more opportunities to detect anomalies, and security teams are thus enabled to discover and counteract abnormalities more quickly.
Serverless Security: The Cons
But serverless security also has to contend with disadvantages: More protocols because the resulting transparency can be assessed as advantages and disadvantages. The resulting openness is undoubtedly an advantage, but getting there involves many protocols: hundreds of functions mean hundreds of protocols.
Many functions can also increase the attack surface because they result in numerous entry points for attackers. Of these, some are more accessible to hackers than others. However, the fine-grained authorization concepts bring maximum control for the functions so that an efficient IAM can reduce the attack surface again.
A disadvantage can also be that fixed company perimeters and data centers as boundaries of the company IT are no longer available. Until now, the inside and outside of a company network were firmly defined – serverless security is changing this perception. Are there limits to each function? In every resource? It is important to explain here, not least, to clarify legal issues.
Serverless Security: Common Mistakes
To understand the advantages, it is essential to avoid a few typical mistakes. For example, it is often assumed that the Web Application Firewall (WAF) takes care of the security of all applications. The WAF is traditionally located at the Internet gateway out of the company infrastructure, and it protects web and application services but does not secure all applications. The WAF inspects HTTPS traffic and covers functions triggered by the API gateway. Events on the cloud network started elsewhere are not protected by the WAF. The WAF should not be understood as the only protection program; Security gaps in the network can be closed with specialized security solutions.
A second common mistake is unedited feature permissions—the permissions discussed in the benefits. Functions should not have more leeway than they need – or vice versa: keep access permissions for positions as low as possible. Please take a look at each function and check what it does and what permissions are required for it. This allows you to configure the roles and access approvals precisely, making subsequent adjustments less time-consuming.
Organizations need to understand further that application code does not necessarily have to be homegrown to adopt serverless security. Cloud applications usually consist of numerous modules and libraries. A module often includes countless other modules, making it clear that a single serverless function combines tens of thousands of code lines from different sources. Many application source codes consist of open-source content. Attackers are increasingly attempting to incorporate malicious code into community projects, and Open-source sites like GitHub can do that. If the new version finds its way into cloud applications, the malicious code comes with it.
Another common mistake is trusting the wrong signs of an attack. As described in the advantages and disadvantages of serverless security, the principal increases visibility and transparency. Since the amount of information is growing massively, some companies have hardly any opportunities to read the data and interpret it meaningfully and comprehensively. Artificial intelligence (AI) and machine learning (ML) help: They can automatically increase security in the cloud and efficiently support employees in evaluating logs.
Recommendations For Serverless Security
Follow the Zero Trust approach to increase security: The company network is segmented, and access rights are strictly restricted. In this way, damage following successful attacks can be limited.
You can use code analysis tools (SCA, see above) to monitor your code and that of others. In this way, you maintain a basic level of security and prevent malicious code from being smuggled in. If you also rely on XDR, you can have your entire IT infrastructure monitored automatically, partly based on AI.
Serverless Security: A New Way With New Concepts
As you can see, serverless security is an exciting approach, but it requires a rethink: Away from rigid company boundaries toward many serverless functions requiring protection. Do not just rely on cloud providers’ full-bodied advertising promises, but examine various options. You should also adapt your IT security strategy to the new architecture – and work as precisely as possible right from the start because only then is security also on board with serverless functions.