What Actually Happens When Your IT System Is Hacked?
Cyber-attacks are a real and persistent threat to businesses. Every week, there are news headlines about yet another data breach or hack. Unfortunately, this is unlikely to change anytime soon. Hackers are getting more sophisticated, and IT security systems must work much harder to keep up. Although hacking is something most of us have heard […]
Data Protection – Our Advice For Working From Home Safely
Since telework is developing rapidly today, professional data security is a more pressing issue every day. These few tips will help you work remotely from home without risk. Protect Network Access Most teleworkers use WiFi, so there is a need to protect network access effectively. Unfortunately, this type of connection is not the most secure […]
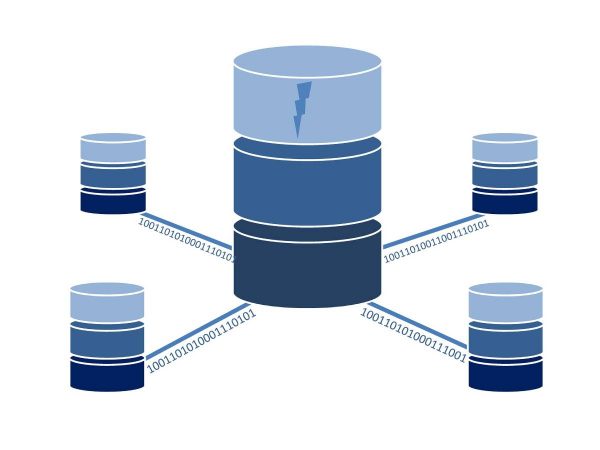
Serverless Security – New Challenges In Securing Applications
The digital transformation brings innovations – sometimes that more and more applications are operated in the cloud. Of course, this has advantages: the maintenance effort, for example, is significantly reduced, which means that costs can also be reduced. But it is also essential to deal with IT security – and we will do that for […]
What’s the Difference Between a Security Operations Center and SIEM?
A security operations center is an essential part of any safely operated network. Many different things are going on inside busy security operations centers. For example, the SOC engineers have significant functions across all the centers, regardless of size. Continual Monitoring, Analysis, and Response Practices Engineers monitor network threats 24 hours a day, seven days […]
These Are The Cybercriminals’ Psychological Tricks
How do hackers get someone else’s access data and passwords? You ask for it. Flattery, dangerous curiosity or misunderstood willingness to help, especially in the run-up to Christmas, can be the door opener. HP names the six most common psychological tricks used by cybercriminals. Social engineering attacks – the art of getting someone to do […]
Cybersecurity Is An Urgent Challenge For Companies
The interest in cybersecurity is increasing, but betting on it to prevent attacks and unexpected threats is still something pending in many companies. Cybersecurity is the set of tools, policies, security measures, and technologies aimed at protecting information assets and users of an organization from malicious attacks or threats in the cyber environment, ensuring that […]
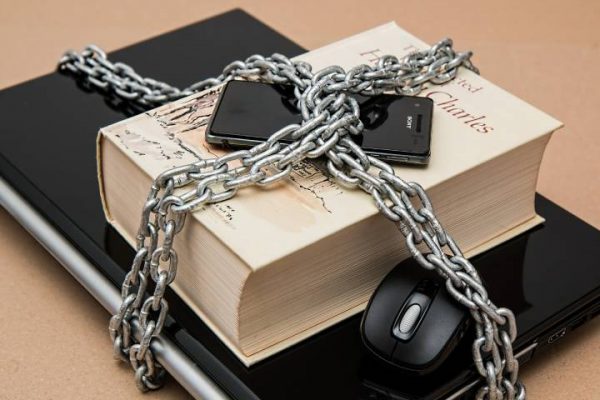
5 Essential Physical Security Measures Your Business Needs to Implement
In 2020 and most of 2021, business security was been a hot topic. We’d been through COVID restrictions and many businesses faced closure for months at a time. This made many business owners turn their attention to various aspects of their business, including their physical security and ensuring that they don’t come under the threat […]
Spy Apps – This Is How You Protect Your Smartphone
Data protection is very important! The rule here is compliance with the General Data Protection Regulation, obligation to publish a legal notice, consent to website cookies, and double opt-in procedures for newsletter registrations. Spying on the data is prohibited and not a trivial offense. This also includes the data on your smartphone. Criminals try to […]
How To Identify Cyber Security Threats At An Early Stage
Cyber security is a major concern for businesses and institutions all over the world. As technology improves, so does the need for cyber security. Hackers are developing sophisticated ways to breach security systems of organizations and companies in a bid to match the standards that such institutions are taking to curb these attacks.To highlight the […]
Identify The Risks In Terms Of Information Security.
Along with technological advances come new concepts, new areas of knowledge, new study niches, and information security. However, we all have some idea about this matter and its importance. But really: What is Information Security? What does it consist of? What Is Information Security? It is the set of mechanisms and activities that we apply […]