Strengthening Enterprise Networks with Advanced Firewall Defense
Understanding the Importance of Firewall Defense Enterprises today face a wide range of cyber threats, from malware to sophisticated network attacks. As organizations grow and adopt new technologies, their digital environments become more complex and vulnerable. A strong firewall defense is essential for controlling access, monitoring traffic, and blocking malicious activity before it can cause […]
Why Security Has Become a Top Priority For Online Bettors?
To demonstrate stable growth, modern betting platforms must address every aspect of user experience. They must not only provide users with the ability to predict a few clicks, but also ensure that this does not compromise the security of their personal data. Digital security is becoming a key topic of discussion among online bettors, as […]
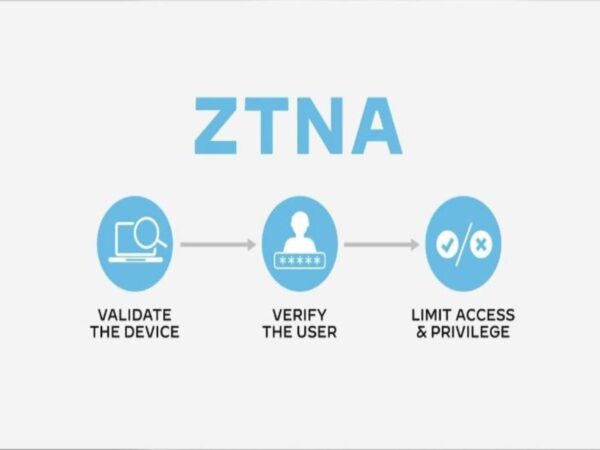
Zero Trust Isn’t a Tool: How ZTNA Is Reshaping Secure Enterprise Access
For a long time, we thought of office security as a giant stone wall: everyone inside the building was safe, and everyone outside was a potential risk. This worked fine when all the computers were plugged into the same wall, and all the data stayed on a server in the basement, but that is not […]
Why Most Application Breaches Exploit Business Logic, Not Code
Security teams spend countless hours and resources hunting for technical bugs. We run static analysis scanners to find SQL injection flaws, we configure web application firewalls to block cross-site scripting (XSS), and we obsess over buffer overflows. We are conditioned to look for flaws in the code itself—the syntax, the libraries, the infrastructure. But what […]
How Hybrid Work Is Reshaping Security and Compliance Strategies
The shift to hybrid work has permanently altered the corporate landscape. Employees now split their time between offices, homes, and various remote locations, creating a distributed workforce that demands fundamentally different security approaches. For UK organisations, this transformation presents both unprecedented challenges and opportunities to reimagine how they protect data and maintain compliance. Traditional security […]
How DSPM Protects Sensitive Customer Data from Hidden AI Risks
These days, businesses increasingly rely on Artificial Intelligence (AI) and machine learning (ML) to improve decision-making, personalize customer experiences, and streamline operations. While these technologies offer tremendous benefits, they also introduce subtle risks that can put sensitive customer data at stake. AI systems process vast amounts of personal and financial information, and without proper safeguards, […]
Cybersecurity Myths Debunked: What You Need To Know
Cybercrime is rife in 2025 and affects businesses of all sizes and in all industries. Cybersecurity should be a priority for all businesses, but there are many that have inadequate protection in place. There are a lot of myths and misconceptions around cybersecurity, which can leave businesses vulnerable. A cyber attack can harm a business […]
A Buyer’s Guide to DSPM Tools
Choosing the right Data Security Posture Management platform takes careful evaluation. Start by understanding your organization’s specific needs and available options. The market has many DSPM tools, each with different capabilities and deployment models.This buyer’s guide to DSPM tools will help you through the selection process. It covers key evaluation criteria, technical requirements, and cost. […]
TekGPS Login – A Comprehensive Guide For Smart GPS Tracking
In This tech driven world everything is digitalized and updated. GPS tracking has also become an essential thing for various businesses and individuals. For fleet management, tracking some valuable assets, logistics and also for tracking your loved ones GPS tracker is a must and should thing. In today’s article we are going to discuss all […]
185.63.2253.200: Everything About This IP Address
In this digital Era IP Address is one of the main components in the internet communication and data exchange between individuals and businesses across the globe. Every internet connection has a unique IP address which can be considered as a unique identifier. All the devices connected to some internet connection will have the same IP […]