Benefits of Using a VPN (Virtual Private Network)
We are still in the days of the Wild West of the Internet, and each click hides a potential danger or exploitation. Right now, tech companies are mining your data and selling it to the highest bidder, not to mention scammers, trolls, thieves, sharks, spies, hackers, and scammers. During this time, you walk around naked; […]
Which Tools Are Used For Ethical Hacking?
Are you looking for a challenging career that helps you strengthen your skills and apply them to solve real-world problems? If yes, then an ethical hacker role might just be the right career choice for you. The role of an ethical hacker requires you to be as tricky as a malicious hacker and close all […]
IT Security – Fit For Managed Security Services In 6 Steps
The trend towards Managed Security Services (MSS) is becoming increasingly apparent. The reason: Many IT departments are now reaching the limits of their performance regarding security since attack scenarios are constantly changing and the handling of security tools is becoming more and more complex. Companies, therefore, call in specialists to avoid risks. Establish A Basic […]
Technological Challenges In Business Strategy In 2022
In this particular 2022 that has changed our lives due to the impact of COVID-19, technology is an important cushion that minimizes the impact suffered by people and companies. This success represents a boost in the digitization of organizations and marks the future roadmap. Technologies that manage to provide greater flexibility will enable companies to […]
Two-Factor Authentication – Opportunity Or Risk?
Double is not automatically better: conscientious handling your data is the be-all and end-all. Two-factor authentication ( 2FA ) is a “strong customer authentication” measure that checks whether an electronic payment transaction is legitimately made. The 2FA consists of a first factor for the identity of a user, which consists of a username and password, […]
The Importance of Videoconferencing Tech
What if you could find a videoconferencing device that could do everything you need it to do? If you have tried other videoconferencing devices, you might have noticed the slight inadequacies that prevent you from having a great user experience. You may spend hours searching for the perfect videoconferencing devices that delivers on-demand. If you are ready to experience […]
Is It Good Practice To Use a Free VPN?
Most people cannot or opt not to pay for a trusted VPN service, so they go for a free VPN service instead. A VPN (a virtual private network) that provides top-level encryption protocols and guaranteed privacy indeed comes with a price. This is why many people go for free VPNs; that can be a risky […]
How To Create A 100% Secure Password
Do you want to be sure that your data, emails, photos and other personal information you keep on the web are protected from malicious people? The first thing to do is watch your accounts well on various websites and providers. In today’s article, I want to show you how to create a 100% secure password, […]
Steps To A Secure Home Office
The home office is more than just the company computer in the living room or bedroom at home. Companies must take special security measures since the systems are not located within the secure office infrastructure. Home offices are now part of everyday life in numerous companies. They will probably remain so since many employees and […]
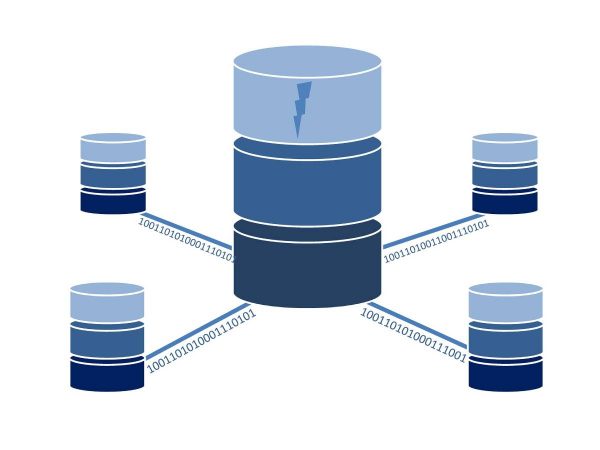
Serverless Security – New Challenges In Securing Applications
The digital transformation brings innovations – sometimes that more and more applications are operated in the cloud. Of course, this has advantages: the maintenance effort, for example, is significantly reduced, which means that costs can also be reduced. But it is also essential to deal with IT security – and we will do that for […]